What is BARTS?
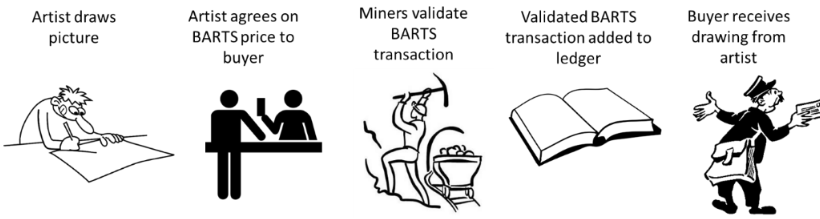
The Blockchain ART Simulation (BARTS) and related experiential online exercises facilitate understanding blockchain concepts. The BARTS simulation is a non-technical simulation where participants mine or validate a digital coin transaction for buying and selling drawings (see Figure 1). Graduate students, undergraduate students, and high school students with technical and non-technical backgrounds have used the simulation to get a clearer idea of blockchain mining concepts.
Simulation participants need laptops, smartphones, or tablets with access to the internet to participate as a cryptocurrency miner. The BARTS simulation has been used with 50 students. But we believe that it can be scaled online to more than 100 students.
Our premise is that understanding the role of secure hashing algorithms in the mining process is the primary conceptual impediment for students to gain an accurate picture of the validation process for blockchain transactions. The BARTS simulation and experiential PHP programs help understand cryptocurrency mining, hashing concepts, proof of work and proof of stake, immutable ledgers, and digital currency value.
BARTS Preparatory Material
- The following paper presents a good overview of the BARTS simulation and experiential exercises. The Blockchain Art Simulation (BARTS) and Experiential Exercises Paper presented at ITiCSE 21 in Paderborn Germany: ITiCSE BARTS Paper
- PowerPoint slides for the instructor on the BARTS simulation: BARTS PowerPoint Slides
- Handout to be given to students on the BARTS simulation: Handout for BARTS Simulation Download
BARTS Mining Programs:
- Here is the mining program to be used by the students: https://tinyurl.com/BARTSMiningV2
- Here is the mining ledger program to be used by the instructor: https://tinyurl.com/BARTSBlockchain
Additional BARTS Exercises
We have found that the BARTS simulation is an excellent way to introduce hashing concepts, but the hashing process needs additional discussion because of its importance to several security concepts. These exercises delve deeper into hashing concepts and were also used as the foundation for developing the BARTS simulation. These exercises were presented at the 34th Annual (CCSC) Eastern Regional Conference in 2018 by Sean Sanders under the title “A-Noncing the Use and Performance of Hashing Algorithms”. The paper received a best student paper award.
- EXERCISE 1 : Generate a nonce that will result in a leading zero for a hash. Nonces are used to change the value of the hash. In blockchain implementations, the nonce is added to the end of the text being hashed to generate a hash with a specified number of leading zeros. Bitcoin currently requires about 19 leading zeros. The difficulty of the mining process is controlled by requiring more leading zeros. Students enter their name with the number 1 right after their name and keep incrementing the number following their name by one more unit until a hash with one leading zero is generated. This program is available at http://104.156.254.129/Exercise1.php
- Exercise 2: A Hashing program that automatically searches for a nonce. This algorithm is complicated because it has to keep searching until it finds a hash with the correct number of leading zeros. Bitcoin miners use specialized hardware capable of generating trillions of hashes per second. This program is available at http://104.156.254.129/Exercise2.html.
- Exercise 3: Mining Computation Issues: The purpose of this exercise is to illustrate in greater detail the computational demand that is required for using hashing for proof of work. It requires participants to enter the text to be hashed, along with the number of leading zeros, then clicks on the hashing algorithm desired and the number of times to run the simulation. The program will find the hash by adding a nonce, or random number, to the string until it generates a hash with the appropriate number of leading zeros. This program is available at http://104.156.254.129/Exercise3.html.
- Exercise 4: Birthday Paradox and cracking secure hash algorithms: The safety of secure hash algorithms is always an issue of interest. The Birthday Paradox can be used as an approximation of the amount of brute force computing necessary to find a hash collision. The program can be found at http://104.156.254.129/BirthdayParadox.php. The number of years needed to find a collision for the lowly 160 bit SHA1 algorithm using 5,000 ASICS computers, each capable of 13TH/s with a total hashing rate of 65,000 TH/s, is 0.74 years. This contrasts with the 208.06 trillion years to find a collision with the SHA256 algorithm using the brute force approach.



Leave a comment